Verify applicant credentials: A step-by-step guide for public safety HR
Hiring the wrong person for a public safety role is not simply an HR inconvenience. It is a liability event, a community safety risk, and in the worst cases, a career-ending scandal for the agency involved. 28% of credentialing errors stem from relying solely on applicant-submitted copies rather than going directly to the source. For law enforcement agencies, fire departments, dispatch centers, and private security firms, that error rate is unacceptable. This guide walks HR professionals and hiring managers through a structured, compliance-grounded workflow for verifying applicant credentials with the rigor that public safety demands.
Table of Contents
- Why credential verification matters in public safety
- What you need: Credential types and requirements
- Step-by-step: Effective applicant credential verification process
- Troubleshooting: Addressing edge cases and credential fraud
- Ensuring compliance: Legal standards every HR team must follow
- The uncomfortable truth: Where most verification workflows break down
- Streamline your verification process with trusted partners
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| PSV is essential | Direct confirmation with issuing authorities prevents costly credentialing errors. |
| Comprehensive compliance | Every verification step must follow federal and state regulations to ensure legal protection. |
| Technology boosts accuracy | Workflow automation and AI tools accelerate verification but require proper oversight. |
| Fraud awareness | Live, multi-source verification and attention to red flags help detect sophisticated scams. |
| Document the process | Maintain audit-ready records of every verification to support legal and accreditation needs. |
Why credential verification matters in public safety
Public safety roles carry a level of trust that few other sectors require. A police officer carries legal authority to arrest, detain, and use force. A paramedic holds lives in their hands. A dispatcher coordinates emergency responses where seconds determine outcomes. When credential verification fails at any of these positions, the ripple effects extend far beyond a single bad hire.
The legal exposure alone is significant. Negligent hiring claims arise when an agency fails to take reasonable steps to confirm an applicant’s qualifications and that employee later causes harm. Courts routinely examine what verification steps were taken, and gaps in documentation are treated as evidence of negligence. The verification risks in public safety that arise from inadequate checks are not hypothetical. They are litigated regularly, and agencies rarely emerge unscathed when their process fails scrutiny.
Beyond litigation, credentialing errors erode public trust in ways that are nearly impossible to reverse. A single high-profile incident involving a officer who falsified training records or concealed a prior decertification can generate months of negative press, trigger state investigations, and undermine community relations that took years to build.
Stat callout: Research shows that non-primary source verification is linked to a 28% error rate in credential files, and the U.S. healthcare sector alone loses $100 billion or more annually to fraud enabled by inadequate background checks. Public safety is equally, if not more, vulnerable.
Key risks agencies must actively manage include:
- Litigation from negligent hiring claims when a verified qualification turns out to be fabricated
- State decertification triggered by discovering an officer’s concealed prior misconduct or revoked POST certification
- Federal compliance violations if FCRA or EEOC protocols are not followed during the screening process
- Reputational damage that affects recruiting, community partnerships, and officer morale
- Direct harm to the public if an unqualified person performs safety-critical duties
The path to reducing hiring risks starts with understanding exactly what needs to be verified and building a process disciplined enough to catch what applicants may intentionally or unintentionally misrepresent.

What you need: Credential types and requirements
Before any verification step begins, HR teams need a clear inventory of what they are checking. Public safety credentialing is broader than most sectors, covering not just education and work history but certifications that are legally required to perform the job, psychological evaluations, and criminal records that may disqualify candidates under state law.
According to the California POST Background Investigation Manual, a thorough background investigation for law enforcement must include verification of education, employment history, licenses and certifications such as POST, criminal records, character references, and National Decertification Index (NDI) checks. The same manual establishes that FBI fingerprint checks, individualized criminal history assessment, and full EEOC compliance are standard requirements, not optional add-ons.
| Credential category | What to verify | Who to contact |
|---|---|---|
| Education | Degrees, diplomas, transcripts | Registrar’s office directly |
| Employment history | Dates, titles, reason for leaving | Previous employers, HR departments |
| POST certification | Active status, any prior revocations | State POST board |
| Criminal records | Arrests, convictions, deferred adjudication | State and federal repositories |
| Professional licenses | Active status, disciplinary history | Licensing board |
| Medical and psych evaluations | Fitness for duty | Licensed examiner |
| References | Character, performance, integrity | Direct contact with listed references |
| NDI check | Prior decertification in any state | IADLEST National Decertification Index |
Understanding background check regulations that govern each of these categories is essential before the process begins. Federal rules such as the Fair Credit Reporting Act (FCRA) apply whenever a consumer reporting agency (CRA) is involved. State background check laws may impose additional requirements around timing, disclosure, and use of criminal history.
Key compliance elements HR teams must build into their process include:
- Written FCRA authorization obtained from the applicant before any check is initiated
- A pre-adverse action notice, along with a copy of the report and a summary of rights, issued before any adverse employment decision
- Individualized assessment performed before disqualifying a candidate based on criminal history
- State POST standards met for each certification category, including timelines for initial verification and renewal cycles
Pro Tip: Build a credential verification checklist that maps each required credential to its primary source and the compliance rule governing it. This single document reduces errors, accelerates onboarding, and creates the audit trail you will need if a hiring decision is ever challenged.
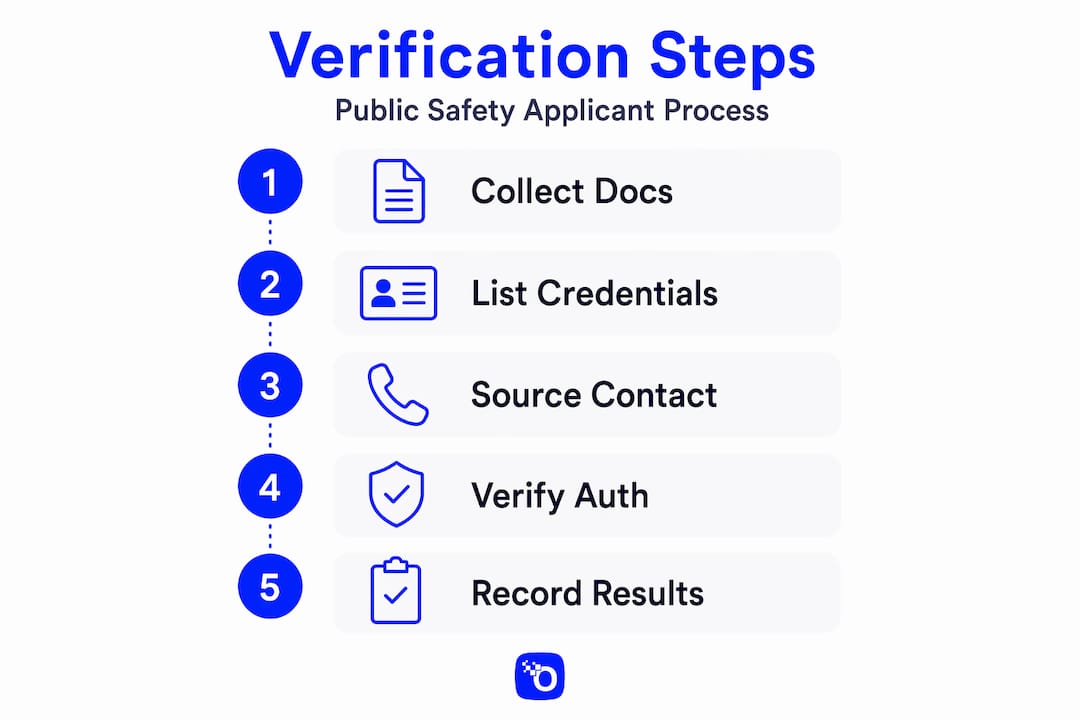
Step-by-step: Effective applicant credential verification process
The difference between a verification process that holds up under scrutiny and one that fails at the first legal challenge almost always comes down to sequence and documentation. Here is a structured workflow designed for public safety HR.
-
Confirm applicant identity first. Before verifying a single credential, confirm that the person you are screening is who they claim to be. Use government-issued photo ID, cross-reference with biometric data where available, and flag any inconsistencies in name variations or date of birth discrepancies across submitted documents.
-
Collect signed FCRA authorization and release forms. Do not initiate any external inquiry until you have valid, dated, written consent. This protects the agency and ensures the process is legally defensible from the start.
-
Begin primary source verification (PSV) for all credentials. Primary source verification means contacting the actual issuing organization, whether a university registrar, a state POST board, or a professional licensing body, rather than relying on copies or third-party summaries. PSV is the gold standard because it eliminates the forgery risk that applicant-submitted documents carry inherently.
-
Contact sources through secure, verifiable channels. Reach out via recognized credentialing methods including secure database queries, direct phone calls to listed institutional numbers (not numbers provided by the applicant), official email requests, and written letters where digital access is unavailable.
-
Run criminal history checks through state and federal repositories. Submit fingerprints for FBI checks, query state criminal databases, and run a National Sex Offender Registry search. For law enforcement candidates specifically, an NDI check through IADLEST is critical to catch officers decertified in other states.
-
Conduct structured reference interviews. Generic reference calls yield generic responses. Use structured questions that probe specific incidents, performance under stress, integrity concerns, and reasons for departure. A well-constructed reference interview often surfaces information that no database can provide.
-
Document every contact, response, and delay. Record the date and method of each inquiry, the name and title of the person who responded, the content of the response, and any follow-up required. Verifying candidate integrity depends as much on the completeness of the audit trail as it does on the accuracy of any single data point.
-
Adjudicate findings against established disqualifying criteria. Review results against your agency’s written standards. For any potential disqualifying finding, apply an individualized assessment before making a final decision.
| Verification method | Speed | Accuracy | Cost | Best for |
|---|---|---|---|---|
| Applicant-submitted copies | Very fast | Low (fraud risk) | Minimal | Pre-screening only |
| Direct institution contact | Moderate | High | Low to moderate | Standard PSV |
| Credential Verification Organizations (CVOs) | Fast | High | Moderate | High-volume hiring |
| Secure database queries | Very fast | High | Variable | Certifications, licenses |
| Structured phone interviews | Moderate | High | Low | References, employment |
Pro Tip: Many agencies underestimate how much a Credential Verification Organization (CVO) can accelerate the process for high-volume or specialized credentials. CVOs maintain ongoing relationships with issuing institutions and can often return verified results faster than direct contact, especially for educational credentials from large universities.
Note that NCQA 2026 standards require most verifications to be completed within 120 days of appointment, though public safety hiring timelines often aim for significantly faster resolution to avoid losing candidates to competing agencies.
Troubleshooting: Addressing edge cases and credential fraud
Even a well-designed verification process will encounter situations that fall outside the standard workflow. Credential fraud has grown more sophisticated alongside the technology available to detect it, and HR teams need to be prepared for scenarios that require heightened scrutiny.
Fake applicants using AI-generated documents and fabricated international credentials represent a growing threat in high-stakes hiring. These are not easily caught by automated screening alone. The documents look professionally produced, the claimed institutions may exist but the records do not, and response times from fraudulent sources can be suspiciously rapid because they are staged rather than genuine.
Common red flags HR investigators should watch for include:
- Digital versus paper discrepancies. A diploma that looks pristine and digitally generated when the institution has only issued paper credentials is a warning sign. Conversely, a scan that shows signs of physical alteration warrants manual review.
- Unusually rapid responses from unfamiliar sources. Legitimate institutions have processing queues. If a response arrives within hours from a rarely contacted institution, verify that the responding party is actually affiliated with the institution through an independent channel.
- Untraceable or newly registered institutions. Diploma mills often operate under names that closely resemble real universities. Verify institutional accreditation through the U.S. Department of Education’s database before accepting any credential from an unfamiliar source.
- Gaps in credentialing timelines. Unexplained multi-year gaps between credentials, especially gaps that align with possible periods of incarceration or decertification, require direct follow-up.
- Inconsistent personal identifiers. Name variations, date of birth discrepancies, or multiple Social Security Numbers linked to a single individual are serious fraud indicators.
“The sophistication of AI-enabled credential fraud means that even experienced investigators can be deceived by visual inspection alone. Live video verification and OSINT (open-source intelligence) reviews are now considered essential tools for high-risk applicant screening.” — Adapted from industry guidance on applicant fraud prevention.
For international credentials, the verification burden is significantly higher. Countries maintain different accreditation systems, licensing bodies, and record-keeping standards. Use recognized foreign credential evaluation services, contact the relevant embassy or ministry of education when necessary, and never accept applicant translations of foreign documents as primary sources.
The National Decertification Index is an often-underutilized resource that every law enforcement agency should query for every sworn officer candidate. It captures decertification actions from participating states and serves as a critical cross-check for candidates who have relocated after losing certification elsewhere. Protecting data privacy in checks while using these databases is equally important. Ensure that any data accessed is handled in compliance with applicable privacy laws and stored securely after the investigation concludes.
Pro Tip: For any candidate whose identity or credentials raise even a minor concern, conduct a live video interview as part of the verification process. This confirms that the person who submitted the application and the person you are considering hiring are the same individual, a safeguard that is especially important when applications are submitted remotely.
Ensuring compliance: Legal standards every HR team must follow
Credential verification in public safety does not operate in a regulatory vacuum. Multiple federal and state frameworks govern what you can check, how you must notify applicants, and how you may use findings in an employment decision. Failing to follow these rules does not just create procedural problems. It creates independent legal liability.
The primary federal frameworks every HR team must understand and apply are:
-
The Fair Credit Reporting Act (FCRA). Any time a third-party consumer reporting agency is used to run background checks, FCRA applies. You must obtain a clear, written authorization from the applicant before initiating any check. If a finding may lead to adverse action, you must provide the applicant with a pre-adverse action notice, a copy of the report, and a written summary of their rights. After a reasonable waiting period, you may then issue a final adverse action notice.
-
EEOC guidelines on criminal history. EEOC guidance prohibits blanket disqualification policies based on criminal records. Before excluding a candidate due to criminal history, HR must conduct an individualized assessment that considers the nature and gravity of the offense, the time elapsed since the offense or sentence completion, and the nature of the job sought. These are sometimes called the Green factors, and ignoring them opens the agency to discrimination claims.
-
State POST standards. Every state with a POST (Peace Officer Standards and Training) board has its own certification requirements, background investigation timelines, and disqualifying criteria. These standards operate alongside, and sometimes more strictly than, federal rules. Confirm the specific requirements for your state and build them explicitly into your verification checklist.
“Compliance is not a box to check at the end of the hiring process. It must be integrated into every step, from the initial application form to the final hiring decision, because a procedural failure at any point can render the entire investigation legally vulnerable.”
- Adverse action protocol timing. Many agencies underestimate the timing requirements embedded in the FCRA adverse action sequence. The pre-adverse action notice must go out before the decision is finalized, and the applicant must be given a reasonable opportunity (typically five business days) to dispute inaccurate information before the final notice is issued.
Maintaining FCRA compliance throughout the process requires training for every staff member involved in hiring, not just the lead investigator. Front desk personnel who handle application materials, HR generalists who communicate with candidates, and supervisors who make final decisions all need to understand what they can and cannot do under federal law.
The uncomfortable truth: Where most verification workflows break down
Here is something that experience teaches quickly: the biggest failures in credential verification are rarely caused by a lack of policy. They happen when policy meets real-world pressure and loses.
Every agency has a credentialing policy on paper. The breakdown happens when a hiring supervisor is three weeks into a critical vacancy and pressures HR to accelerate the process. It happens when a well-liked candidate’s file has a minor discrepancy and no one wants to be the person who delays the hire over a technicality. It happens when automation is trusted to catch everything, and the edge cases it cannot handle slip through unnoticed.
Technology aids including AI and digital credentials can significantly accelerate verification workflows, but they require robust oversight, trained operators, and clear escalation protocols. An automated system that flags potential fraud is only as effective as the human reviewer who knows what to do with that flag. Too many agencies implement technology and then reduce the human oversight that makes the technology meaningful.
Primary source verification is the element most commonly skipped under time pressure. It is also the element most likely to catch fraud. When agencies skip PSV and rely on applicant-supplied documents or secondary verification summaries, they are essentially accepting the applicant’s word that their credentials are genuine. That is precisely the gap that proper vetting is critical to close.
The other systemic failure point is documentation quality. Investigators who conduct thorough verbal inquiries but record only summary notes leave the agency exposed. A detailed, contemporaneous record of every contact, every response, every discrepancy investigated, and every judgment call made is the agency’s primary defense in any future legal challenge.
Sustainable verification quality requires three things that no platform can fully replace: continuous quality assurance reviews of completed investigations, regular training for all staff involved in the hiring process, and genuine organizational buy-in from leadership that treats verification as a non-negotiable standard rather than an administrative hurdle. When leadership signals that speed matters more than thoroughness, the entire system degrades accordingly.
Streamline your verification process with trusted partners
Credential verification at the standard public safety demands is resource-intensive, legally complex, and increasingly threatened by sophisticated fraud. Agencies that try to build this capability entirely in-house often find themselves managing fragmented workflows, inconsistent documentation, and compliance gaps that only become visible when challenged.
OMNI Intel’s pre-employment screening platform is purpose-built for exactly this environment. From law enforcement and fire departments to dispatch centers and private security firms, the platform delivers investigator-driven background checks for public safety that integrate FCRA-compliant workflows, primary source verification, NDI checks, and continuous post-hire monitoring into a single, auditable system. If your agency is ready to eliminate the manual gaps and legal exposure that come with fragmented verification, OMNI Intel’s pre-employment investigations give you the structure, speed, and compliance confidence your hiring process needs.
Frequently asked questions
What is primary source verification (PSV), and why is it important?
PSV means confirming credentials directly with the issuing organization rather than accepting applicant-provided copies, and it is the most reliable way to prevent fraud. PSV is the gold standard for credentialing because it eliminates the risk that forged or altered documents will pass undetected.
How long does the applicant credential verification process usually take?
Timelines vary by credential type and method, but NCQA 2026 standards require most verifications to be completed within 120 days. Public safety agencies often complete the core verification faster when using a CVO or integrated screening platform.
What are the federal compliance requirements for background checks?
HR must obtain written FCRA consent before initiating any check through a consumer reporting agency, and EEOC guidance requires an individualized assessment before disqualifying an applicant based on criminal history rather than applying a blanket exclusion policy.
How should agencies handle international credentials?
International credentials require validation through recognized foreign credential evaluation services, direct contact with the foreign institution or relevant government ministry, and heightened document authenticity review. International credentials require extra scrutiny because accreditation systems and record-keeping standards vary widely across countries.
What are typical red flags in credential verification?
The most common red flags include discrepancies between digital and traditional records, unusually fast responses from unfamiliar institutions, applicant-provided contact numbers for verification sources, unexplained gaps in credentialing timelines, and inconsistent personal identifiers across submitted documents.